We often judge AI through a human lens, comparing its intelligence, reasoning, and even emotions to our own. But intelligence is not a single, clearly defined concept, and human thinking is just one model shaped by our constraints and experiences.
AuthorLi_in
Hackthon 2026
This is the new Open Source Hackathon !!
Test event
Test description
AS3W – Access String Authorization (Conceptual)
AS3W (Access String: Who, What, When) is a lightweight authorization mechanism associating access rules directly with data stored in a database.
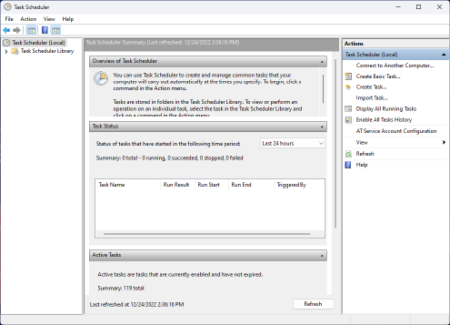
Session Hijacking via Task Scheduler
When a privileged domain user (for example, a Domain Admin) is interactively logged on to a Windows server, a local administrator on that system can leverage the Windows Task Scheduler to achieve code execution inside the user’s logon session.
Playbooks Incident Response — Référence CERT
🔐 AD Reconstruction Phase 0 — Immédiat (0–2h) · Confinement initial # Action Domaine Criticité 0.1 Désactiver ou restreindre tous les accès VPN entrants Réseau 🔴 Critique 0.2 Bloquer tout le trafic entrant et sortant non essentiel (règles firewall d’urgence) Réseau 🔴 Critique 0.3 Activer le geo-fencing sur le firewall (restreindre aux pays autorisés) Réseau
REDTEAM – File Transfer
File transfer is a critical capability during red team operations, whether for payload delivery, data exfiltration, lateral movement, or post-exploitation tooling.
Search for large file on Windows with Powershell
This powershell command allows you to search and list large files in your windows file system. Very useful if you want to save space.
Conversion avec l’IA : L’idolatrie des êtres humains
Pourquoi les humains idolâtrent et pourquoi certains y sont plus réceptifs que d’autres ? L’idolâtrie est un phénomène universel : sportifs adulés, célébrités vénérées, leaders politiques suivis aveuglément, fandoms passionnés…Pourtant, derrière cet attachement intense se cache une mécanique psychologique profonde, parfois saine, parfois dangereuse.Comprendre pourquoi nous idolâtrons — et pourquoi certains y sont plus vulnérables
The Last Invention | How AGI Could Redefine Humanity
Artificial General Intelligence (AGI), the ability of machines to think, learn, and act with the versatility of a human mind is no longer science fiction. While current AI systems remain specialized, the trajectory of research and investment makes the emergence of AGI plausible within this century. The implications extend far beyond automation: AGI has the